Modern digital security relies heavily on encryption algorithms grounded in difficult math problems, which is the backbone of what’s known as public-key infrastructure (PKI). From securing websites to protecting messaging apps, PKI allows two strangers online (or a client and a server) to establish secret keys and verify identities without having met. This is achieved through asymmetric cryptography (public/private key pairs) that current computers find infeasible to break. For example, algorithms like RSA and elliptic-curve cryptography (ECC) underpin much of today’s secure internet traffic, but the advent of quantum computing threatens to upend these protections.
A sufficiently powerful quantum computer could solve those “impossible” math problems in a tractable time, essentially cracking RSA/ECC encryption that would take classical computers hundreds, thousands, or even millions of years. Disturbingly, Shor’s quantum algorithm can theoretically break all widely deployed public-key schemes, meaning that encrypted data intercepted today could be decrypted in the future once quantum computing has advanced to a certain level. This is known as “Harvest Now, Decrypt Later.”
It’s important to note that threats to encryption aren’t limited to quantum computing, either. In theory, a breakthrough in computer science, such as if the famous P vs NP problem were resolved with P=NP, could also dismantle current cryptography. Such a discovery would imply that there exist efficient algorithms for solving problems believed to be hard, like factoring or discrete log, which would make most modern cryptography obsolete. This, though, is considered unlikely in the near term, whereas quantum computing is a tangible development with advancements happening every day in the field.
Because of this looming threat, researchers have been developing what are known as “post-quantum” cryptography (PQC) schemes. These are new encryption and signature methods built on math problems believed to withstand quantum attacks. PQC is now maturing as a field, with standards emerging after years of evaluation. The promise is that these quantum-resistant algorithms could secure data against applications of Shor’s algorithm, though they come with caveats. Many PQC algorithms have larger keys or slower performance, and being relatively new, they lack decades of real-world testing. Should you start using post-quantum encryption for things like VPN connections or stored files? The answer is: it’s complicated.

Related
Quantum computing could help us build a brighter (and greener) future
Looking to the future of computing
Symmetric and asymmetric encryption
A primer on what’s vulnerable
There are two major forms of encryption in use today; symmetric encryption and asymmetric encryption, with the latter relying on PKI principles in its implementation. Both have upsides and downsides, but they’re tailored to different uses.
Symmetric encryption uses one secret key for both encryption and decryption (for example, AES or ChaCha20 ciphers). Symmetric algorithms are fast and well-understood, and the good news is that symmetric cryptography is not severely threatened by quantum algorithms. There is no known “Shor’s algorithm” equivalent for cracking a symmetric cipher outright. The main quantum attack applicable, Grover’s algorithm, could speed up brute-force key search, but it only provides a quadratic advantage, which effectively halves the key’s strength. This is mitigated by using larger key sizes. For instance, Grover’s algorithm would reduce AES-128 (128-bit key) to an effective 64-bit strength, which is a problem, but AES-256 (256-bit key) would be reduced to a roughly 128-bit strength, which remains astronomically hard to crack. In short, your symmetric encryption (if using sufficiently long keys) is already essentially “quantum-safe”, and this typically applies to full-disk encryption and password vaults.
Asymmetric encryption (public-key algorithms) involves a key pair: a public key for encryption or signature verification and a private key for decryption or signing. This category includes RSA, Diffie-Hellman, and ECC schemes, which form the basis of key exchange and digital certificates on the internet. These systems rely on effectively one-way mathematical problems (like factoring large numbers or discrete logarithms), known as “trapdoors.” Shor’s algorithm running on a large quantum computer can solve those underlying math problems in polynomial time, essentially breaking the trapdoor. That means a quantum computer could derive an RSA private key from the public key, or compute the secret in an elliptic-curve Diffie-Hellman key exchange, in a matter of hours or days. All the familiar public-key algorithms (RSA, DH, ECDSA/ECDH, and more) would no longer be secure given a powerful enough quantum computer.
This is a huge problem because asymmetric cryptography is used to set up most encrypted channels today, such as your VPN negotiating a session key or your browser verifying a website’s identity via its digital certificate. As already mentioned, one major concern is that someone could record encrypted traffic now and decrypt it later once quantum capabilities have reached the level required. Unlike symmetric encryption, where a bigger key can counter quantum-based attacks, there’s no simple tweak to enhance security. Entirely new algorithms are needed.
In this scenario, the confidentiality of a VPN tunnel or HTTPS session could be compromised if the attacker can break the RSA/ECDH key exchange that established the session key, even if the actual data was encrypted with AES. Similarly, a digital signature (such as an RSA-signed certificate or code signature) could be forged if the attacker can invert the mathematical problem behind it.
Post-Quantum Cryptography is already in use
It’s just not widely deployed yet
Post-quantum cryptography refers to cryptographic algorithms designed to be secure against an adversary equipped with a quantum computer. These are drop-in replacements for current public-key algorithms, serving the same purposes (key exchange, digital signatures, and more) but built on math problems that even quantum algorithms can’t easily solve. Research into these alternatives started in the 2000s, and efforts were quickly increased once it became clear that practical quantum computers, while not here yet, were no longer purely theoretical.
In 2016, the U.S. National Institute of Standards and Technology (NIST) opened a public project to evaluate and standardize PQC algorithms. Dozens of proposals from academia and industry underwent cryptanalysis “battle testing” over multiple rounds, analogous to a previous AES and SHA competition that was announced in 2007 and completed in 2012. By 2022, NIST announced the first set of winners to be standardized as PQC algorithms.
The algorithms selected by NIST cover two main categories: encryption (key-establishment) schemes and digital signature schemes. Notably, all the primary selections are based on mathematical problems believed to resist both classical and quantum attacks, such as lattice problems or hash functions, rather than factoring. These are:
CRYSTALS-Kyber (ML-KEM): This is a lattice-based key encapsulation mechanism (KEM) used for encrypting session keys (intended to replace RSA/ECC for key exchange). It boasts strong security and efficiency with relatively small public keys and ciphertexts, while also maintaining good performance.
CRYSTALS-Dilithium (ML-DSA): This is another lattice-based digital signature scheme for signing messages, certificates, and more. Dilithium produces signatures on the order of a few kilobytes and uses similarly sized public keys. It was chosen as the primary post-quantum signature standard due to its balanced security and implementation simplicity, without the need for any special hardware.
FALCON (FN-DSA): Yet another lattice-based signature scheme, which has smaller signature sizes than Dilithium but relies on more complex math like floating-point arithmetic. It will be standardized as an alternative signature, which is particularly useful in contexts where smaller signatures are important. This draft standard, FIPS 206, has not been released yet, though it was planned for late 2024.
SPHINCS+ (SLH-DSA): This is a stateless hash-based signature scheme. Its signatures are quite large (tens of kilobytes), and it’s slower, but it’s based on conservative hash assumptions. NIST selected SPHINCS+ as a backup digital signature method in case an unforeseen weakness is found in lattice-based schemes.
There are also additional candidates undergoing standardization, such as HQC, which is an alternative to ML-KEM that uses different math. This ensures that if a weakness in ML-KEM is found, there’s a backup readily available.
These new algorithms aim to replace things like RSA, ECDH, and ECDSA in our protocols. For example, a TLS handshake in a post-quantum world might use Kyber/ML-kEM to agree on a secret key instead of an elliptic-curve Diffie-Hellman, and use a Dilithium/ML-DSA-based certificate instead of an RSA/ECDSA certificate. While the PQC algorithms chosen by NIST have been vetted for security against known quantum and classical attacks, they’re not just drop-in replacements without trade-offs. One challenge is that most post-quantum algorithms have larger key and message sizes than the classical algorithms they replace. For instance, according to Cloudflare, a Kyber-encrypted message will be about 1.5 KB larger than an equivalent ECDH exchange using Curve25519. As well, digital signatures like Dilithium can add tens of kilobytes in overhead if used naively; in one experiment, replacing the standard TLS certificates and handshakes with Dilithium increased the handshake data by roughly 17 KB.
Plus, there’s a question of both confidence and maturity. RSA and ECC have withstood decades of intense cryptanalysis and real-world attacks. By contrast, the new PQC methods are relatively young and not yet as battle-tested. It’s not quite the case that they are believed to be insecure, and in fact, some early contenders were broken or weakened during the competition. However, early adoption carries the risk that unforeseen implementation bugs or minor cryptanalytic breakthroughs could surface once they are deployed at scale.
The practical integration side of things is a massive hurdle. Software and hardware systems have to be updated to support the new algorithms. Many protocols assumed small key sizes and may need adjustments for bigger ones, and both sides of a communication (client and server, or sender and receiver) must support the PQC algorithm to use it, which complicates a gradual transition. At the very least, standards bodies and big industry players have already begun experimenting with PQC in the real world. As well, hybrid TLS handshakes that include a post-quantum KEM (like Kyber) have been tested alongside traditional key exchanges in many major browsers, like Google Chrome and Firefox, though the latter has it disabled by default.

Related
How to use the FileVault encryption feature on macOS
FileVault encrypts the data on your Mac’s startup disk to help prevent unauthorized access. Here’s what you need to know about it.
What’s at risk?
It depends what you do
So, we’ve established what kinds of algorithms are at risk, but what are the real-world applications of these algorithms? We’ll use WireGuard as an example, which is a VPN protocol used in anything from Tailscale to NordVPN (NordLynx). WireGuard uses a fixed set of cryptographic primitives (the Noise protocol framework with Curve25519 elliptic-curve Diffie-Hellman, ChaCha20-Poly1305 symmetric encryption, and Blake2 hashing). When two WireGuard peers connect, they perform a handshake using asymmetric cryptography (ECDH) to agree on a shared secret key, then use that symmetric key to encrypt all subsequent traffic. However, that initial key exchange is exactly the kind of asymmetric operation that a quantum computer could compromise. An eavesdropper who records the handshake could later use a quantum computer to solve the Curve25519 Diffie-Hellman problem, recover the shared secret, and thus decrypt the entire session’s traffic.
To make matters worse, the peers’ long-term public keys in WireGuard (used to authenticate each other) are also based on ECC, so a quantum attacker could potentially forge identities or impersonate servers by deriving private keys from public ones. So, how can this be made safe? In protocols like TLS, one approach is to perform a hybrid key exchange: an example being to do the regular ECDH and a post-quantum key exchange in parallel, then use both results to derive the session key. But WireGuard’s simplicity is a double-edged sword here, as it was intentionally designed without cryptographic agility or negotiable algorithms. The creator of WireGuard has suggested an interim fix: use the protocol’s optional pre-shared key (PSK) feature as a quantum-resistant add-on. This means using a static symmetric key known only to the two peers; this PSK is mixed into the handshake along with the usual ECDH. Because this pre-shared key is purely symmetric, it isn’t vulnerable to quantum algorithms.
If you use WireGuard, should you worry? In most cases, VPN traffic is ephemeral, with the sensitivity of the traffic diminishing as time passes. If you don’t expect an attacker to record your VPN traffic and value it years down the road, you don’t need to panic. In enterprise settings, another approach is to overlay an additional quantum-safe encryption layer inside the VPN, such as a post-quantum TLS connection through the VPN for particularly sensitive sessions. Some VPNs that use WireGuard, like NordVPN, are opting to use ML-KEM for a PSK exchange.
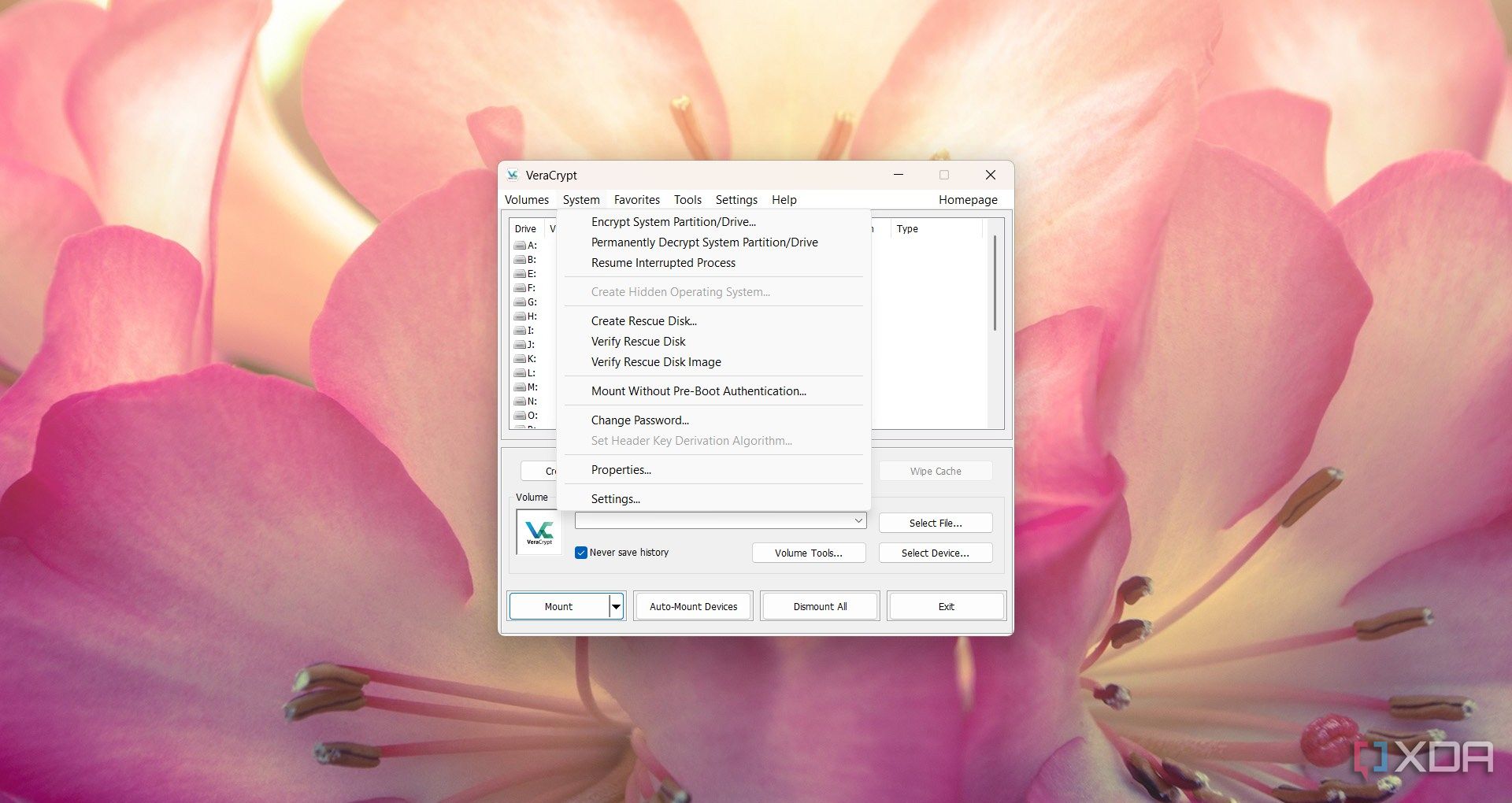
As for full disk encryption (FDE), these systems also predominantly use symmetric cryptography, and the same goes for password vaults. The disk encryption itself is not the weak link under quantum; it’s the key and how it’s derived. When you encrypt a drive with VeraCrypt or a similar tool, you set a passphrase, and the software uses a KDF (PBKDF2, or other algorithms) to derive a 256-bit key that encrypts the disk. If the disk is encrypted with AES-256, a quantum computer would face the daunting challenge we described earlier to brute force that key, effectively a 128-bit security problem after Grover’s algorithm, which is still out of reach for any foreseeable technology.
VeraCrypt, for example, uses AES-256 and PBKDF2 with a high iteration count for the header key derivation as a default, providing a fairly high margin of security. Some users may opt to cascade multiple ciphers (VeraCrypt allows chaining AES, Serpent, and Twofish), and this can further increase the security margin while also providing user confidence that they’re protected against unknown future attacks. But strictly speaking, a single strong cipher with a 256-bit key is already believed to be quantum-resistant, as long as the key itself remains secret.
For typical use, there’s no direct quantum weakness in FDE implementations like VeraCrypt. Continue to use strong passwords, and consider changing your encryption keys every so often (meaning you should decrypt and re-encrypt the drive with a new key) if you want to be extra safe for decades-long data protection. But realistically, if a nation-state adversary is storing your encrypted hard drive for 15 years in the hopes of decrypting it later with a quantum computer, you’re probably worrying about bigger threats at that point.
Do you need PQC right now?
It depends who you are
The answer to this depends on who you are and what your threat model looks like. For the average person using a VPN for privacy or using a tool like VeraCrypt for storing personal files, there’s no immediate need to panic or change anything. Your priority should be to follow current best practices, and in the latter case of file storage, there’s nothing to worry about in the interim at all. If you’re worried about quantum threats, the most practical step is to ensure you’re using at least 256-bit keys for symmetric encryption (which most apps do by default now) and avoid deprecated algorithms. Plus, operating systems and tools will be updated over time to protect against those quantum threats in the background.
If you’re in a potentially targeted position, though, then that changes somewhat. Organizations that handle sensitive data with a long shelf life should absolutely be preparing for a post-quantum transition now. Industry experts and bodies like Gartner predict that by around 2029, advances in quantum computing may leave current public-key crypto completely unsafe, and they advise treating 2029 as a deadline to have quantum-safe solutions in place. NIST expects similar. By 2030, it expects organizations (especially those in critical infrastructure or government) to have transitioned away from RSA-2048 and comparable ECC to the new PQC algorithms, and its guidance will change to entirely disallow their use in 2035.
To be clear, transitioning will take years, so starting to transition now is a good idea, especially given the immense effort required and the potential for roadblocks in deployment. Waiting until the last minute (say 2028 or 2029) could be too late, given the risk of “harvest now, decrypt later” attacks already looming, and those in positions where the secrecy of data still matters in five or even ten years should consider transitioning sooner rather than later.
For most personal needs, current encryption provides more than enough protection and will gradually evolve to PQC without you needing to do anything drastic. It’ll likely all happen in the background, and ideally, most normal users will never even notice the transition while still being kept safe online.