AI coding agents run with shell access, environment variables containing API keys, and unrestricted internet connectivity, creating a single point of failure where one compromised tool call can leak credentials to an attacker-controlled domain.
Pipelock, an open-source security harness developed by Joshua Waldrep under the PipeLab project, addresses this exposure by inserting an enforcement layer between agents and the network. Version 2.3.0 shipped with class-preserving request redaction and generic SSE streaming response scanning.
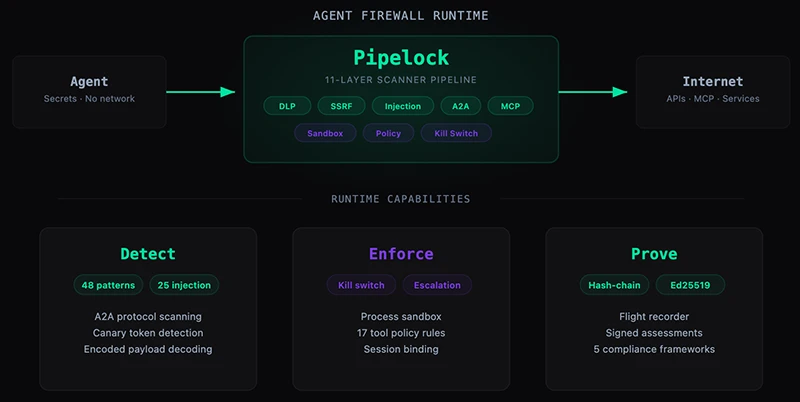
Architecture and scanning pipeline
Pipelock runs as a single Go binary of roughly 20 megabytes with 22 dependencies, distributed under the Apache 2.0 license. The design relies on capability separation: the agent process holds the secrets and operates without direct network access, the proxy holds network access and no secrets, and all traffic crosses a scanning boundary between the two zones. Network isolation depends on deployment-level controls such as network namespaces, iptables, Docker internal networks, or Kubernetes NetworkPolicy.
Waldrep, the developer behind Pipelock, draws a distinction between the project and the broader category of agent-security tooling. ŌĆ£Most agent-security tools still need the agent to cooperate. They are SDKs, decorators, middleware, or wrapper APIs the agent has to call. Those controls only work while the agent keeps calling them,ŌĆØ he told Help Net Security. He added that a steered or poisoned agent can skip the very controls meant to watch it, which is why Pipelock sits outside the agent at the egress boundary. He compared the arrangement to how TLS handles trust on the web, where the component being verified is separate from the component producing the proof.
Every request flows through an 11-layer scanner pipeline covering scheme enforcement, CRLF injection detection, path traversal blocking, domain blocklisting, data loss prevention, path and subdomain entropy analysis, SSRF protection, rate limiting, URL length checks, and per-domain data budgets.
The DLP layer covers 48 credential patterns including API keys, tokens, financial account numbers, and cryptocurrency private keys, with four checksum validators (Luhn, mod-97, ABA, and WIF) to suppress false positives. Encoding-aware decoding handles base64, hex with six delimiter formats, URL encoding, and Unicode evasion. Response scanning applies 25 injection detection patterns with six normalization passes for zero-width characters, homoglyphs, and leetspeak. The system fails closed: timeouts, parse errors, oversized bodies, and unscannable compressed content all default to block.
Coverage and evidence features
The proxy scans HTTP forward proxy traffic, CONNECT tunnels, WebSocket frames in both directions, Model Context Protocol stdio and streamable HTTP transports, and Google Agent-to-Agent protocol messages. Audit output takes the form of a hash-chained tamper-evident log with optional Ed25519 signatures, supplemented by signed assessment bundles and CycloneDX 1.6 agent bills of materials.
Compliance mappings cover the OWASP MCP Top 10, OWASP Agentic AI Top 10, MITRE ATT&CK technique IDs, EU AI Act runtime controls, SOC 2 control families, and NIST 800-53. SARIF v2.1.0 output integrates with GitHub Code Scanning.
Roadmap
Waldrep said the signed evidence receipt format is already implemented and ships with a Python reference that independently recomputes the canonical preimage and validates the signature, producing a byte-identical result to the Go implementation. ŌĆ£The push from here is making that format public infrastructure for agent attestation: more language SDKs, broader transport coverage, and getting external auditors to check Pipelock evidence with their own tooling,ŌĆØ he said. The goal, he added, is a primitive other vendors and open-source projects can emit and consume.
Pipelock is available for free on GitHub.

Must read:

Subscribe to the Help Net Security ad-free monthly newsletter to stay informed on the essential open-source cybersecurity tools. Subscribe here!

